Go to you kids right now and ask them if they know what cyberbullying is. Go on, do it! I’m going to guess that they might be able to tell you at least something. If they did, that is encouraging.
Now ask them if they know what sexting is. Heck that word shows up in my spell check as being unknown or misspelled. I will bet you that your older kids know what it is but that your younger ones do not.
Here’s one more that even I didn’t know about (well, I know about the definition but not the actual name for the process): “grooming“. Just ask them what the term “grooming” means. I asked my 3 kids of various ages (8, 10, 13) if they knew what the term meant. Not one of them knew so it was a good dinner time educational experience.
I have said it time and time again, you need to spend time with your children in order to help them understand the dangers of the wild, wild internet. Since I have 3 girls, who are all pretty tech savvy, I have to be sure that they are protected on each and every device that they use, have restrictions applied based on their age, and talk with them about the dangers of online strangers (and strangers in general).
Remember that no matter what you do from an education standpoint, doing absolutely nothing is the worst thing you can do. You may have the latest and greatest piece of online protection software, but you would be surprised at how kids can learn how to bypass it. They almost think of it as a challenge or obstacle to get around. However, if you explain to them the reasoning for having protection as well as the dangers that exist and that you are doing it not to restrict them, but to protect them, hopefully they will understand and then the challenge of bypassing melts away.
Before I do a quick walk through of another nice tool from Trend Micro called Online Guardian for Families, let’s talk a little bit about the 3 terms that I mentioned at the beginning: cyberbullying, sexting and grooming.
Cyberbullying was a term that each of my kids have at least heard of and they were able to articulate what part of the definition is. They were able to tell me that it has to do with bullying using a computer. But I tried to expand on that definition to include mobile devices as well. The definition, according to Trend Micro, is: “The use of information communications technology (particularly mobile phones and the Internet) to deliberately upset someone else.”
Schools are pretty good about teaching about bullying. But nowadays, bullying has been taking to an increasingly harder level to manage – on the internet and mobile devices. Whereas in the past, you typically had to be physically present to bully, with cyberbullying, you have the “advantage” of electronic delivery of bullying information. That is to say, if an “incriminating” picture is sent around via social media or mobile, it can be distributed faster and to more people.
Cyberbullying can take the forms of:
- Calls or text messaging that may include threats or harassment.
- Sharing of humiliating images.
- Taking movies of others being bullied and sending them to other sites or phones
- Using instant messaging to sent nasty messages or spread rumors.
- Using a chat room to pretend to be someone else in order to spread rumors.
- Creating fake profiles on social media in order to pretend to be someone else to get the other person in trouble.
Download more information on Cyberbullying here.
Sexting is another new term that is a combination of texting and sex. It is the act of sending sexually explicit messages or photographs (even movies) between mobile devices. The danger of sexting is that any of the messages or photos that are sent, can be copied and/or resent and can be an integral part of Cyberbullying. Children need to understand that the distribution of “sexual” content can fall under child-pornography laws and the content that is created can be used to bully someone else.
Lastly is a term that I had never heard about – “online grooming.” When I asked my kids if they have heard of this phrase, they told me that they hadn’t, which is a bit surprising since there is a lot of education that takes place at school. However, since my kids didn’t know the exact meaning of the term, it was a perfect opportunity for me to talk to them about it.
To use the Trend Micro definition, “‘grooming’ is the way sexual predators get from bad intentions to sexual exploitation. Basically, grooming is manipulation. It’s the process pedophiles use to get young people they target online to meet with them offline, the simple goal being sex.” But how to do explain that to an 8 year old. Trust me, it’s pretty hard answering “Why would they want to do that” questions.
But the important thing is to make sure that they understand the cues and clues that are out there. Trend Micro has put together a very good document that provides you with example tactics and other resources that you can use for more information. To summarize some of the tactics, here’s what you need to let you child know to look for:
- Requests to “go private” – these predators like getting their victims isolated and away from the public
- Using flattery – frequently these predators employ many different types of flattery to make the victim feel much better and trust them more.
- Sympathy – these predators appear sympathetic to allow the groomer raise the subjects comfort level.
Another thing that Trend Micro has put together is a questionnaire that is broken out by age group of your child to gage how much they do or do not know about the terms above as well as Internet safety in general. It’s a good icebreaker to get you and your children engaged in a conversation about this serious subject matter. I recommend downloading it and printing it out and then the next time you are having dinner with your kids (e.g., a captive audience), you start asking them some of these questions. The questionnaire can be downloaded here.
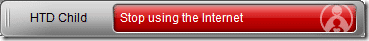
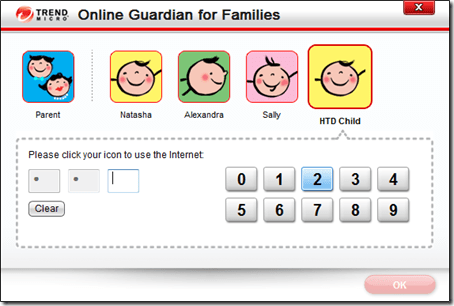
Lastly, there are lots of different types of ways that you can provide levels of protection for your kids, some basic ones are free while other may have a monthly or yearly subscription. I have actually tried quite a few of them out and feel that regardless of which one you choose, anything is better than not using any type of online monitoring at all. The one from Trend Micro called Online Guardian for Families, allows you to set up various profiles for your children and then deploy these monitoring and blocking software out to any Windows-based computer that you have installed Online Guardian on. When a child logs into an account on one of these computers, they are ask for a personal identifier (a PIN) and then their profile is loaded. If they go over the pre-set amount of time, or try to access the internet “after hours” or try to access a site that they are not allowed to, they are blocked and the parent notified.
The biggest mistake that you can make when it comes to Internet security for your children is doing absolutely nothing at all! So, take a few minutes to download the questionnaire and then be sure to go through explaining to them about the questions and the importance of being careful online.
Disclosure Text: For the Digital Joneses Study, Trend Micro has provided each of the bloggers involved, including me, technology and/or software items for use in the various challenges and/or for review. I have a material connection because I received these items for consideration in preparing to write this content. I was/am not expected to return these items or gifts after my review period or the study duration. All opinions within this article are my own and not subject to the editing or approval by Trend Micro or its contractors. More information can be found in my About page as well as here.
HTD says: Your children are your most valuable possession! You need to be sure to educate them well, especially when it comes to online predators!


1 comment
Carol Cain
Awesome, awesome post!